
I absolutely love giving presentations! I love to run my mouth, so being able to do so in front of like-minded individuals is a passion of mine. I’ve started to lose track of the various presentations I’ve given, so I made this page to catalogue my work and provide resources should anyone be interested in reviewing the content.
If you are a CISO, I have a few presentations on the SANS CISO Network’s OnDemand platform. You can learn more about joining the SANS CISO Network at https://www.sans.org/mlp/ciso-network/.
Table of Contents
Featured
PikaBot Malware Analysis: Debugging in Visual Studio – John Hammond’s YouTube channel [2024.02]
Recording here: https://www.youtube.com/watch?v=k2rH0ISuMwE — video embedded below
Hands-on Ransomware: Exploring Cybercrime – John Hammond’s YouTube channel [2023.05]
Recording here: https://www.youtube.com/watch?v=9zEXov_L0os — video embedded below
Detecting & Hunting Ransomware Operator Tools: It Is Easier Than You Think! – Community Night SANS Secure Australia 2023 [2023.03]
View live stream details and recordingRyan Chapman, SANS Instructor and author of SANS FOR528: Ransomware for Incident Responders, provides an overview of tools leveraged often by ransomware operators. Though a multitude of ransomware operations and affiliate groups exist, we see a great deal of overlap between the tools leveraged by these groups (and that’s an understatement!).
- Are you following and utilizing projects such as Living Off Trusted Sites (LOTS) and Bring Your Own Vulnerable Driver (BYOVD)?
- Do you know how PsExec-like tools work at a forensic level (e.g., smbexec)? Are you hunting for rogue installations of Remote Monitoring & Maintenance (RMM) tools?
- Did you know that data exfiltration tools like Winzip, 7Zip, WinSCP, FileZilla, Rclone, and MEGAsync often leave forensic artifacts that are absolute snitches that are just phenomenal for us cyber defenders?
In this session he will discuss these tools, and show you how they work, and share tips & tricks related to preventing, detecting, and hunting them!
Recording here: https://www.youtube.com/watch?v=oMAvSpq9fYY
Slides and Japanese recording available here: https://www.sans.org/webcasts/community-night-sans-secure-australia-2023-detecting-hunting-ransomware-operator-tools-its-easier-than-you-think/
Stay Ahead of Ransomware LIVEstream Series – Ep. 1: The Top 5 Misconceptions About Ransomware [2023.03]
View live stream details and recordingAttend this SANS LIVE session to learn about the top five common misconceptions pertaining to ransomware. Many people believe that they and/or their org need not worry about ransomware. Unfortunately, ransomware is pervasive and anyone reading this may end up on the wrong side of an attack. For example, ransomware operators commonly hit companies of sizes 11-100 employees. Organizations from many different industries, not just those considered “critical,” may find themselves on a victim list. We’ll provide an overview of what’s truly happening with ransomware and end with a Q&A session so that YOU can ask us questions.
Recording here: https://www.youtube.com/watch?v=ekdpO4oBiv0
The Truth about Ransomware: Its not Complicated! [2023.01]
View Webcast details and recordingThe threat of ransomware now permeates our daily computing lives. News stories of attacks have become ubiquitous. While media outlets often portray ransomware attacks as advanced operations carried out by highly skilled threat actors, this often is not the case. In fact, the opposite is true — Many ransomware attacks are opportunistic and leverage insecure configurations to enter an environment. These groups are not stealthy, in fact they are often quite loud.
For example, most ransomware attacks involve multiple groups including initial access brokers (IABs), paid “pentester” affiliates, the ransomware malware authors, money mules, and more. The bulk of IABs and third-party affiliates are more akin to thieves who test door handles to find an opportunity vs. those who slink around in the shadows and cut holes in glass to enter buildings. In this talk, Ryan Chapman and Rob Lee discussing how to keep these groups out, how to detect them once they’re in your network, and how to respond should the worst-case scenario occur. Thwarting ransomware isn’t rocket science, it just takes awareness and diligence, so let’s push to ensure we’re all ready for what’s ahead.
Recording here: https://www.youtube.com/watch?v=8xAuvl0Cp90
Learning to Combat Ransomware: An Overview of the NEW SANS FOR528 Course
View Webcast details and recordingOur new SANS DFIR course, FOR528: Ransomware for Incident Responders, is geared toward the Incident Responder in all of us. The course begins with the history and inner-workings of ransomware campaigns. We then move to a highly hands-on, lab-focused environment in which we learn about how ransomware operators engage in all cycles of the attack lifecycle. We cover tooling, detection methods, data collection for response, hunting for operators, and more. Join us for our first live-stream event in which we detail the course and provide an overview of what you can expect. Join SANS Author and instructor Ryan Chapman for this live stream as he introduces this new SANS Institute course.
Recording here: https://www.youtube.com/watch?v=8FGIyV12aVU
Monti Ransomware: Is It a Doppelganger or a Pivot? — LinkedIn Live [2022.09]
View Webcast details and recordingConti and Monti: What’s the deal? They may sound similar, but is there actually any relationship between the two ransomware groups? And how worried should you be about protecting your organization from this new threat Conti?
Watch the latest episode of BlackBerry LIVE as Most Distinguished Threat Researcher Dmitry Bestuzhev and his guests unpack what the BlackBerry team discovered about Monti. For this episode of our live stream video show, Bestuzhev hosts Principal Incident Response & Forensics Consultant Ryan Chapman, and BlackBerry Principal Threat Researcher Anuj Soni.
“Evidence has revealed that this may actually not be a mockery [of Conti], but rather this may be another part of the evolution of the Conti crew,” explains Chapman. Also during the broadcast, our guests explain: 1) The relationship between Monti and Conti 2) Tricks and tools the threat actors used to accomplish their dirty deeds & 3) How they discovered and defeated Monti.
Recording here: https://www.youtube.com/watch?v=0uGHHPxyeQQ
Read the related blog post: https://blogs.blackberry.com/en/2022/09/monti-ransomware-is-it-a-doppelganger-or-a-pivot
Have Fun with It!: Tracking Ransomware Operator Lateral Movement and Recovering Deleted Files the Easy Way! — ResponderCon [2022.09]
View Webcast details and slidesRansomware sucks! We all know that. Even though it annoys us, we cannot simply ignore the threat. Should a ransomware incident occur (including an encryption event or not), you will need to track lateral movement, identify tools/scripts used, and even analyze forensic artifacts to identify deleted files. In this talk, Ryan will be covering two open source tools (free ftw!) that you can leverage to identify lateral movement and analyze malicious data from a system, even when that data has been deleted. Would you like to generate a visual graph of threat actor movement throughout a network? All you need are some Security.evtx files, easy right? Would you like to recover scripts, malicious tool output, and more, even if that data has been deleted? All you need are the MFT and UsnJrnl files. Also easy, right? Yup! Easy mode ftw!
Recording here: https://www.youtube.com/watch?v=moLX5enW3Ek
Slides available here: https://respondercon.io/wp-content/uploads/2022/09/Ryan_Chapman_Have_Fun_with_It_Tracking_Ransomware_Operator_Lateral_Movement_and_Recovering_Deleted_Files_the_Easy_Way.pdf
Keynotes
Much Ado About Ransomware — US Secret Service’s National Computer Forensics Institute Ransomware Training Week [2021.10.11]
View presentation PDFNo recording available
SANS Presentations
Healthcare Ransomware Discussion — SANS 2nd Annual Healthcare Forum [2023.10]
View Webcast details and recordingRyan Chapman joins SANS 2nd Annual Healthcare Forum to discuss ransomware.
Ryan has worked in the Digital Forensics & Incident Response (DFIR) realm for over 10 years. He is the author of the new SANS course on ransomware FOR528: Ransomware for Incident Responders and he has also taught the SANS FOR610: Reverse Engineering Malware. During his career, Ryan has worked in Security Operations Center and Cyber Incident Response Team roles that handled incidents from inception through remediation.
— Tackling Cyber Threats in Healthcare The importance of cybersecurity in patient safety has never been more prevalent. Organizations face ever evolving threats to their complex systems and devices that put patient safety and privacy at risk. Join us for our 2nd Annual Healthcare Forum as we explore the industry’s leading cybersecurity topics from the skilled practitioners defending against threats. Learn More: https://www.sans.org/mlp/sans-healthc…
Recording here: https://www.youtube.com/watch?v=Olmv9aDoZ_8
Security Isn’t Just a Job, It’s a Lifestyle: Tips for Ransomware Prevention — SANS Security Awareness Livestream [2022.10]
View Webcast details and recordingCybersecurity Awareness Month is in full swing and the team at SANS Security Awareness is up to their usual fun and games to keep cyber safety front of mind. This October, we turn our attention to ransomware with a number of programs and activities focused on ransomware awareness and prevention.
Ryan Chapman is a SANS Certified Instructor with a passion for researching ransomware to help as many people as possible learn to deter, detect, and respond to it. This passion has led him to create the upcoming SANS course, FOR528: Ransomware for Incident Responders. We can think of no one better to have present his thoughts on this pervasive threat.
Join Ryan on Tuesday, October 11 at 1pm EDT for a live – and lively – discussion on what he considers to be best practices for ransomware prevention from a security awareness perspective including tips for password hygiene, phishing avoidance, and device security.
Recording here: https://www.youtube.com/watch?v=TAylWDdLDms
SANS Institute – Anatomy of a Ransomware Operation — On-demand Webinar [2022.10]
View Webcast details, recordingRansomware has changed significantly, even over the past few months. If you’re still thinking about ransomware as a drive-by download with a single-system impact, that’s an outdated perception. Ransomware deployments today are disruption operations designed to inflict maximum pain on the victim organization. They typically have a single goal: getting the victim to pay by any means necessary.
Watch On-Demand, SANS Senior Instructor Jake Williams, SANS Instructor, and BlackBerry Principal Professional Services Incident Response Consultant Ryan Chapman as they dissect and analyze today’s typical ransomware operation. They will look at the eight stages of a modern ransomware operation and much more and close with advice on detection and prevention.
See Jake Williams’ associated whitepaper here: https://blogs.blackberry.com/en/2022/10/anatomy-of-a-ransomware-attack-8-stages-of-operation-white-paper
Register to view the recording here: https://www.blackberry.com/us/en/request/cyber/resources/2022/wb/wb-sans-anatomy-of-a-ransomware-operation
Ransomware and Healthcare. Ew. — SANS Healthcare Forum 2022: Vulnerabilities and Mitigation Techniques [2022.09]
View Webcast details and recordingJoin us for the SANS Healthcare Forum 2022: Vulnerabilities and Mitigation Techniques. This exciting, live stream event is taking place Friday, September 23rd from 10am to 2pm ET. Hosted by SANS Director of Content Marketing, Stephen A. Hart, this event features some of the top minds in healthcare cybersecurity including:
Rob Lee “Security Strategy”
Jason Tugman “Healthcare Policies and Governance”
Ryan Chapman “Ransomware”
Ken Hartman “Threat Landscape and Digital Transformation”
Irina Singh “Security as a Business Enabler”
Stephen Mathezer “Healtchare-specific HIoT, IoT, and OT Vulnerabilities”
Note: Panel included at the end of the summit. Fun talk!
Recording here: https://www.youtube.com/watch?v=rPGQK1Eo8OM&t=3317s
Threats & Challenges 2021: What Cyber Defenders Need to Know – and Do — SANS Blue Team Summit 2021 [2021.09]
View Webcast details and recordingTalk not yet online; will update
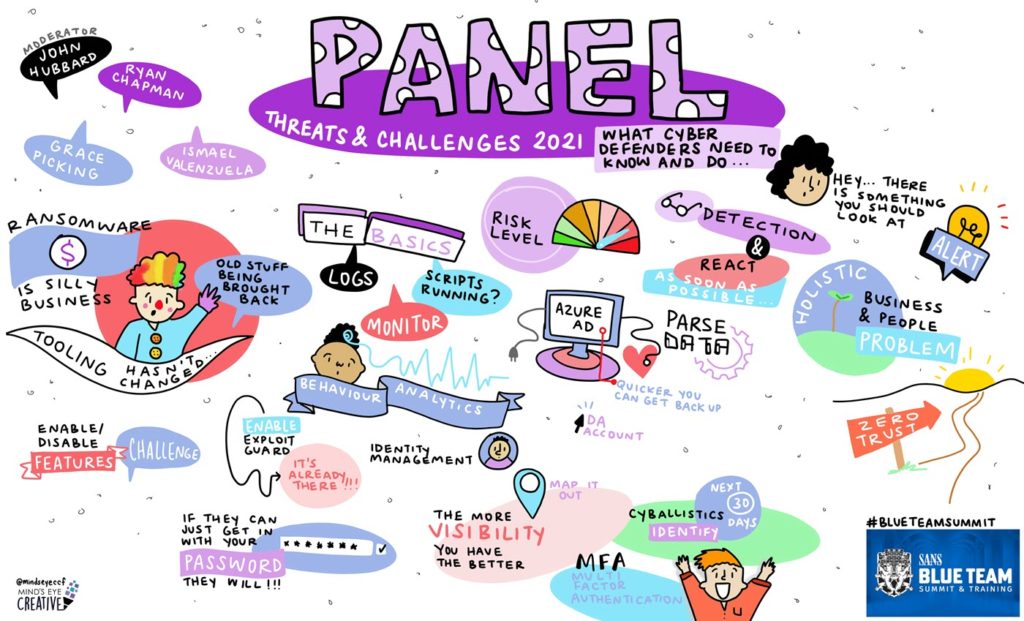
Visual summary from: https://www.sans.org/blog/a-visual-summary-of-sans-blue-team-summit-2021/
Ransomware, Security Awareness, and YOU! — SANS Security Awareness Summit 2021 [2021.08]
View Webcast details and recordingLet’s talk about ransomware; one of the largest threats to organizations around the world. The security awareness team can be a critical piece to the puzzle when it comes to developing, implementing, and carrying out a solid ransomware prevention plan. In this talk we’ll discuss what ransomware is, how it works, and how it can be prevented via fostering vigilance within the organization. We’ll also discuss how the security awareness team can take part in the response effort should a ransomware incident occur, and more. View upcoming Summits: http://www.sans.org/u/DuS Download the presentation slides (SANS account required) at https://www.sans.org/u/1iaE
Recording here: https://www.youtube.com/watch?v=p2Xur8Uzaiw&list=PL_zMFkM-50Ua3dU1Hg7oD5rmPbE05R9Jw&index=5
Visual summary here: https://www.sans.org/blog/a-visual-summary-of-sans-security-awareness-summit-2021/
SANS Threat Analysis Rundown – Ransomware with guest speaker Ryan Chapman [2021.06.30]
View Webcast details and recordingJoin SANS Certified Instructor Katie Nickels as she gives the rundown on the latest threats you should be pay attention to and answers your questions about threat intelligence.
This month, she is joined by Ryan Chapman, SANS Instructor and author of the upcoming course FOR528: Ransomware for Incident Responders (https://www.sans.org/u/1f94) . Katie and Ryan will chat about open sources they use to track the many threats in the ransomware ecosystem, including malware families that commonly lead to ransomware.
Learn more about the FOR528: Ransomware for Incident Responders course here: https://www.sans.org/u/1f94
#ransomware #malware #cyberthreat #cyberthreatintelligence #analysis #OSINT #DFIR #ransomware
Recording here: https://www.youtube.com/watch?v=PmiksJmo6O0
STAR Live Streaming Series details here: https://www.sans.org/mlp/star-webcast/
See also: https://www.sans.org/blog/recommended-sources-for-ransomware-information/
Executives and Ransomware: Stop, Collaborate, and Listen! – SANS Webcast [2021.06.24]
View Webcast details and recordingIn this discussion, James Shank of Team Cymru and Ryan Chapman of SANS will present the top seven themes for ransomware preparedness. Ransomware has become a pervasive threat in todays world. Everyone is aware of the threat, but that doesn’t always translate into Executives knowing what to do to position their organizations well should the threat become reality. You’ll leave this talk with a checklist that will enable your senior technical and security staff to ensure your company is well-positioned to combat this threat. Join us for a lively discussion and come prepared to take notes!
Recording here (currently down for editing): https://www.youtube.com/watch?v=Hq1L6lTnSxw
SANS Webcast details and RECORDING here: https://www.sans.org/webcasts/executives-ransomware-stop-collaborate-listen-120150
Ransomware – Do You Pay It Or Not? – Experts debate the costs ethics around paying ransomware – SANS Webcast [2021.06.03]
View Webcast details and recordingTo pay ransomware attackers or not to pay? The global cybersecurity community continues to debate this complicated issue recently brought to the forefront by the Colonial Pipeline attack. Governments around the globe are now weighing in on what they believe to be the right response to a ransomware attack. Some are even considering making ransomware payments illegal. Putting potential legal requirements aside, on the business side the decision to pay or not to pay isn’t an easy one to make: On one hand, paying ransom encourages additional brazen attacks; on the other, organizations that choose not to pay the ransom may have to shutter operations or find themselves in the position of being unable to pay employees.
SANS is proud to host what is sure to be a dynamic debate of this issue. We’re bringing together some of the top minds in cyber and ransomware incident responders to represent both sides of the debate. Our expert panelists will share stories from the field and their own experiences in responding to what amounts to hundreds of ransomware incidents between the lot of them.
There’s no great solution here — it’s a real-life ‘no-win situation’ for cybersecurity. This debate will focus on providing practical and thoughtful advice that’s based on real-world experiences dealing with ransomware. If you have a strong opinion on the issue, join us to see if you can be swayed. As these unique perspectives will highlight, the decision to pay the ransom or not is much more challenging than you might suspect.
Recording here: https://www.youtube.com/watch?v=L8Au8AmU51I
Spanish version: https://www.youtube.com/watch?v=7sGvMPvHLmk
Portugese version: https://www.youtube.com/watch?v=7sGvMPvHLmk
SANS Webcast details and recording here: https://www.sans.org/webcasts/ransomware-do-you-pay-it-or-not-experts-debate-the-costs-and-ethics-surrounding-ransomware-payments/
Ransomware – Do You Pay It Or Not? – Experts debate the costs and ethics surrounding ransomware payments – SANS Webcast [2021.06.03]
View Webcast details and recordingTo pay ransomware attackers or not to pay? The global cybersecurity community continues to debate this complicated issue recently brought to the forefront by the Colonial Pipeline attack. Governments around the globe are now weighing in on what they believe to be the right response to a ransomware attack. Some are even considering making ransomware payments illegal. Putting potential legal requirements aside, on the business side the decision to pay or not to pay isn’t an easy one to make: On one hand, paying ransom encourages additional brazen attacks; on the other, organizations that choose not to pay the ransom may have to shutter operations or find themselves in the position of being unable to pay employees.
SANS is proud to host what is sure to be a dynamic debate of this issue. We’re bringing together some of the top minds in cyber and ransomware incident responders to represent both sides of the debate. Our expert panelists will share stories from the field and their own experiences in responding to what amounts to hundreds of ransomware incidents between the lot of them.
There’s no great solution here — it’s a real-life ‘no-win situation’ for cybersecurity. This debate will focus on providing practical and thoughtful advice that’s based on real-world experiences dealing with ransomware. If you have a strong opinion on the issue, join us to see if you can be swayed. As these unique perspectives will highlight, the decision to pay the ransom or not is much more challenging than you might suspect.
Recording here: https://www.sans.org/webcasts/ransomware-pay-not-experts-debate-costs-ethics-surrounding-ransomware-payments-119960
Avoiding or Minimizing Ransomware Impact to the Bottom Line: A Panel Discussion – SANS Webcast [2021.05.27]
View Webcast details and recordingOn this webcast, John Pescatore, SANS Director of Emerging Security Trends, and Benjamin Wright, lawyer and SANS Senior Instructor, will discuss key ransomware issues and analyze their associated ransomware report with sponsor representatives.
…
Ryan Chapman, Principal Incident Response Consultant for the BlackBerry Security Services Team, is an IR consultant with roots in SOC and CIRT work. He handles incidents requiring network activity analysis; researching host and network IOCs; hunting through log aggregation utilities; sifting through packet captures; analyzing malware; and performing host and network forensics. Ryan is also the lead organizer for CactusCon, teaches FOR610 for SANS, and is writing a new ransomware-based course for SANS. He also spends time with his family and plays plenty of Street Fighter. Hadouken!
Recording here: https://www.sans.org/webcasts/avoiding-minimizing-ransomware-impact-bottom-line-panel-discussion-118435/
Ransomware Defense 101: A Simple Action Plan – SANS Healthcare Lightning Summit 2021 [2021.05.19]
View Webcast details and recordingThe targeting and theft of sensitive health information continues to be a challenge. Increased regulation combined with a dynamic threat landscape requires health care leaders to have a clear understanding of relevant legislation and how to measurably defend patient data and related systems. This Lightning Summit aims to provide a quick readout from leading experts and support you with practical advice for stopping even the most advanced attacks that may target your health care organization.
YouTube video here: https://youtu.be/3g1Z8TIoZ8E?t=2400
Recording here: https://www.sans.org/webcasts/healthcare-lightning-summit-119555
Oh You Silly Framework!: An Intro to Analyzing .NET Malware – SANS Sydney 2020 @Mic Webcast [2020.11.04]
View Webcast details and recordingMalware written using Microsoft’s (MS’s) .NET Framework operates differently from your standard compiled Portable Executable (PE). The framework, often pronounced “dot net,” provides modern, functional, and easy-to-use assemblies for creating current-generation software. Once the C Sharp (C#), Visual Basic (VB.NET) or other .NET language is compiled, the result is MS Intermediate Language (MSIL). Upon being executed, the MSIL-based PE uses a just-in-time (JIT) compiler to generate native code, which is what we see run when .NET software/malware executes. Wonderfully for both the malware hobbyist and reverse engineering guru alike, MSIL PEs are easily decompiled back to source code. In this talk, SANS Instructor Ryan Chapman will provide an overview of the .NET framework, discuss malware families known to depend upon the framework, and provide analysis methodologies and tools for ripping these samples apart with ease.
Register for free recorded content here: https://www.sans.org/webcasts/silly-framework-intro-analyzing-dotnet-malware-sansatmic-sydney-117015
LOCKED OUT! Detecting, Preventing, & Reacting to Human Operated Ransomware – SANS Webcast [2020.10]
View Webcast description and detailsHuman Operated Ransomware (HORA) threat groups are growing in number and strength every day. In this Webcast, SANS Instructor Ryan Chapman will cover the evolution of, tactics inherent to, and threats associated with HORA. Ryan will provide “quick wins” that you can implement now to protect yourself against this ugly threat. Ryan will also focus on what to do if ransomware is running *right now*, along with what to do when ransomware has run and the outlook is bleak. Ryan will wrap up the Webcast with a list of digital forensics and incident response tools that work well within on-prem and cloud-based environments alike. Are you and your company prepared for this looming threat?
Hunting Human-Operated Ransomware Operators – SANS Threat Hunting & Incident Response Summit 2020 [2020.09.11]
View Webcast details and recordingThe real threat of ransomware these days lies in “Human Operated Ransomware” attacks, in which we see the deployment of ransomware move to secondary or tertiary objectives. The human operators often focus on enumerating the internal environment in preparation of data exfiltration. By the time the ransomware is deployed, the threat actors have already carried out their initial objectives (and stolen your data!). This talk focuses on finding these operators while they are in your network. Find the operators == stop the ransomware deployment.
CactusCon & BSides Talks
Implementing a Kick-Butt Training Program: Blue Team GO! – BSides San Francisco & CactusCon 2019
View talk details and recordingOperationalizing Cyber Threat Intelligence (CTI): Pivoting & Hunting – CactusCon, 2018
No recording available
Exposing the Neutrino EK: All the Naughty Bits – BSides Las Vegas 2016
View talk details and recordingGitHub repo with files: https://github.com/rj-chap/ExposingNeutrino
TAPIOCA: How to Automate Yourself Out of a Job – BSides Las Vegas 2015
View talk details and recordingThese days, many security groups want to become ‘intel shops,” and threat intelligence is all the rage. An intel shop should ingest intel, analyze indicators, and pivot from correlated data. However, few understand how to begin the transition. How IS this accomplished? MAGIC, DAMNIT. Then again, if you’re not the slight of hand kind of guy or gal, we have an answer for you. Check behind your ear, and you’ll find a dollop of TAPIOCA! In this talk, we will present our process for analyzing Indicators of Compromise (IOCs) at scale, correlating information from multiple sources, and pivoting to obtain information from deep within the bowels of our global network. We’ll talk about the technical challenges we have addressed in applying automated analysis to terabytes of data every day. We will also discuss the next-steps for this analysis, including applying machine learning techniques to help further classify our data. We are also releasing our automated IOC vetting tool, TAPIOCA (TAPIOCA Automated Processing for IOC Analysis), to help other security groups begin processing and benefiting from threat intelligence.
Misc Presentations
Black Hat Research Preview – Linux Threats: A Black Hat 2022 Hot Topic? — LinkedIn Live [2022.08]
View Webcast details and recordingJoin BlackBerry’s Ismael Valenzuela, Vice President, Threat Research & Intelligence; Dmitry Bestuzhev, A Most Distinguished Threat Researcher, and Ryan Chapman, Principal Incident Response & Forensics Consultant, as they discuss Linux threats they’re seeing these days and preview their upcoming BlackHat USA presentations.
Recording here: https://www.youtube.com/watch?v=Swos5he5sc4
See the associated blog post here: https://blogs.blackberry.com/en/2022/08/linux-threats-a-black-hat-2022-hot-topic
Protecting Your Workforce from Business Email Compromise – BlackBerry Webinar [2020.10.27]
View Webcast details and recordingJoin BlackBerry for an informative webinar on safeguarding your workforce from business email compromise and other business critical services for remote workers.
Ryan Chapman, BlackBerry Principal Consultant, Incident Response & Digital Forensics, walks through:
– Tips for securing your business email
– Business email compromise (BEC) threats and how to avoid them
– The evolution of phishing attacks from malware deployment to credential theft
– How BEC attacks should be analyzed and reported
– How a BEC Assessment can help you understand your email-based threat landscape
Don’t miss this valuable presentation on ways to address the threats facing remote workers. Watch this webinar on-demand now.
The official, On-demand webinar is available here: https://blogs.blackberry.com/en/2020/10/webinar-protecting-your-workforce-from-business-email-compromise
A modified version of the webinar is also available on YouTube:
Incident Response in Your Newly Expanded Workforce – Nth Generation Symposium 2020
No recording available
Threat Hunting in 2020: Focal Points for Success – SINC Virtual Roundtable New York/New Jersey
View Webcast details and recordingLink: https://sincusa.com/event/blackberry-virtual-roundtable-new-york-new-jersey/
Sign up at the link above to view recording
IT Security Outlook 2020: What to Expect in the Year Ahead – eSecurity Planet 2020
View Webcast details and recordingLink: https://globalmeet.webcasts.com/starthere.jsp?ei=1276480&tp_key=c653ee8eb5&sti=cylance
Sign up to view on-demand.
Threat Intelligence – Buzzword or Buzz-Worthy? – Cisco Threats: The Good, the Bad and the Ugly 2018
View Webcast details and recordingJavaScript Deobfuscation
MalWerewolf: JS/Shellcode Deobfuscation
View YouTube recordings (part 1 & 2)Splunk Talks
PowerShell Power Hell: Hunting for Malicious PowerShell with Splunk – Splunk.Conf 2016
View talk recordingSecurity Operations Use Cases: ‘Cause Bears, Pandas, and Sandworms – Splunk.Conf 2015
View talk recordingSecurity Operations Use Cases: ‘Cause Bears, Pandas, and Sandworms – Splunk Live! Santa Clara 2014
Same as Splunk .Conf 2015 preso above
Security Operations: Hunting Wabbits, Possum, and APT – Splunk Live! Scottsdale 2014
View talk slidesSlides available here: https://www.slideshare.net/Splunk/bechtel-customer-presentation-61159932
Security Operations Center Use Cases – Splunk Live! Phoenix 2013
My first InfoSec talk!! Alas, no recording available.
Cyber Forensics Workshop
This is a 6-part workshop that I presented to students from Cal State University Fullerton (CSUF) back in 2014. While the version of WireShark we use is quite old, the content is still completely viable here in 2021-2022.
View workshop recordings from YouTube (all 6 parts!)